
Years in Business
Expert penetration testing revealing weaknesses attackers exploit to compromise organizations.
As a specialized provider of penetration testing services serving security-conscious organizations worldwide, we specialize in simulating sophisticated cyber attacks that test the resilience of your security controls, identify exploitable weaknesses, and validate the effectiveness of your defense mechanisms across complex digital environments.
We understand that effective security testing transcends automated vulnerability scanning; it requires human ingenuity, adversarial thinking, and deep technical expertise. Our penetration testing methodology combines ethical hacking techniques with systematic reconnaissance, exploitation, and post-exploitation analysis to mirror real-world threat actor behaviors.
We deploy certified penetration testers with credentials including OSCP, CEH, CREST, and GPEN who leverage frameworks such as OWASP, PTES, and NIST to execute thorough security assessments. Each engagement delivers comprehensive findings documentation, risk prioritization, and strategic remediation roadmaps.
Whether you need compliance-driven testing for PCI DSS, HIPAA, or SOC 2 requirements, or proactive security validation to defend against advanced persistent threats, our penetration testing services deliver the technical depth and business context necessary to transform security from reactive protection into strategic advantage.
As security experts specializing in offensive testing methodologies, we deliver targeted penetration testing services that systematically evaluate every layer of your technology stack. Our comprehensive approach ensures no vulnerability remains hidden, giving you complete visibility into exploitable weaknesses across networks, applications, cloud infrastructure, and human defenses.
We assess your Internet-facing infrastructure to identify exploitable vulnerabilities in perimeter defenses, public-facing services, and network configurations. Our testing includes reconnaissance, port scanning, service enumeration, vulnerability exploitation, and privilege escalation attempts that simulate external attacker methodologies targeting your organization.
Our internal security assessments evaluate controls from an insider perspective, simulating compromised employee accounts or physical breaches. We perform lateral movement testing, privilege escalation, Active Directory exploitation, and data exfiltration simulations to reveal weaknesses in segmentation and access controls.
We execute comprehensive web application security assessments following OWASP methodology, identifying injection flaws, broken authentication, sensitive data exposure, and business logic vulnerabilities. Our manual testing approach discovers complex issues that automated scanners cannot detect, ensuring your applications withstand sophisticated attacks.
Our mobile app security testing covers iOS and Android platforms through static and dynamic analysis techniques. We identify insecure data storage, inadequate cryptography, improper session handling, and API vulnerabilities while testing against OWASP Mobile Top 10 standards for comprehensive mobile security validation.
We evaluate RESTful and GraphQL APIs for authentication bypass, authorization flaws, injection vulnerabilities, and excessive data exposure. Our API assessments identify business logic flaws, rate limiting issues, and integration weaknesses that could compromise backend systems and sensitive data repositories.
Our cloud-focused security evaluations assess AWS, Azure, and GCP environments for misconfigurations, excessive permissions, and insecure architectures. We evaluate identity and access management, storage security, network segmentation, and compliance posture to ensure your cloud deployments maintain robust security boundaries.
We identify vulnerabilities in wireless infrastructure through comprehensive testing of WiFi encryption, authentication mechanisms, rogue access point detection, and client isolation. Our wireless security testing exposes weaknesses in WPA2/WPA3 implementations, captive portals, and guest network segregation that attackers could exploit.
Our social engineering assessments test human vulnerabilities through realistic phishing campaigns, vishing attempts, and physical security testing. We measure susceptibility to manipulation tactics, evaluate security awareness effectiveness, and provide targeted training recommendations to strengthen your human firewall against sophisticated social attacks.
We conduct sophisticated, multi-layered attack simulations combining technical exploitation, physical security testing, and social engineering. Our red team exercises provide realistic adversary emulation that tests detection capabilities, incident response effectiveness, and organizational resilience against advanced persistent threats.
Our specialized testing evaluates Internet of Things devices, industrial control systems, and embedded hardware for firmware vulnerabilities, insecure communications, and physical attack vectors. We identify weaknesses in device authentication, encryption implementations that could enable unauthorized access or device compromise.
We deliver penetration testing services aligned with regulatory requirements including PCI DSS, HIPAA, SOC 2, ISO 27001, and GDPR. Our compliance testing provides audit-ready documentation, validates control effectiveness, and ensures your security program meets industry-specific standards and regulatory obligations.

As a globally recognized provider of penetration testing services, we deliver technical excellence, certified expertise, and proven methodologies that consistently identify critical vulnerabilities across complex enterprise environments. Our team comprises certified ethical hackers holding credentials with extensive real-world experience in offensive security and threat intelligence.
Effective penetration testing demands more than tool execution; it requires adversarial creativity, deep technical knowledge, and business context awareness. Our security professionals combine systematic testing frameworks with innovative attack techniques to discover vulnerabilities that conventional assessments overlook. We follow industry-standard methodologies while adapting our approach to your unique environment and risk profile.
Security and confidentiality remain paramount throughout our engagements. We implement strict rules of engagement, maintain detailed activity logs, and protect all findings with comprehensive non-disclosure agreements. Our testing minimizes operational disruption through careful scoping, coordinated scheduling, and continuous communication with your technical teams.
By choosing us as your penetration testing partner, you gain strategic advisors committed to strengthening your security posture through actionable intelligence, transparent reporting, and ongoing support that transforms testing findings into measurable risk reduction across your digital infrastructure.
Years in Business
Projects Delivered
Client Relationships

Investing in professional penetration testing services delivers measurable business value beyond simple vulnerability identification. Our comprehensive security assessments provide strategic intelligence that reduces risk exposure, strengthens compliance posture, and builds stakeholder confidence in your security program.
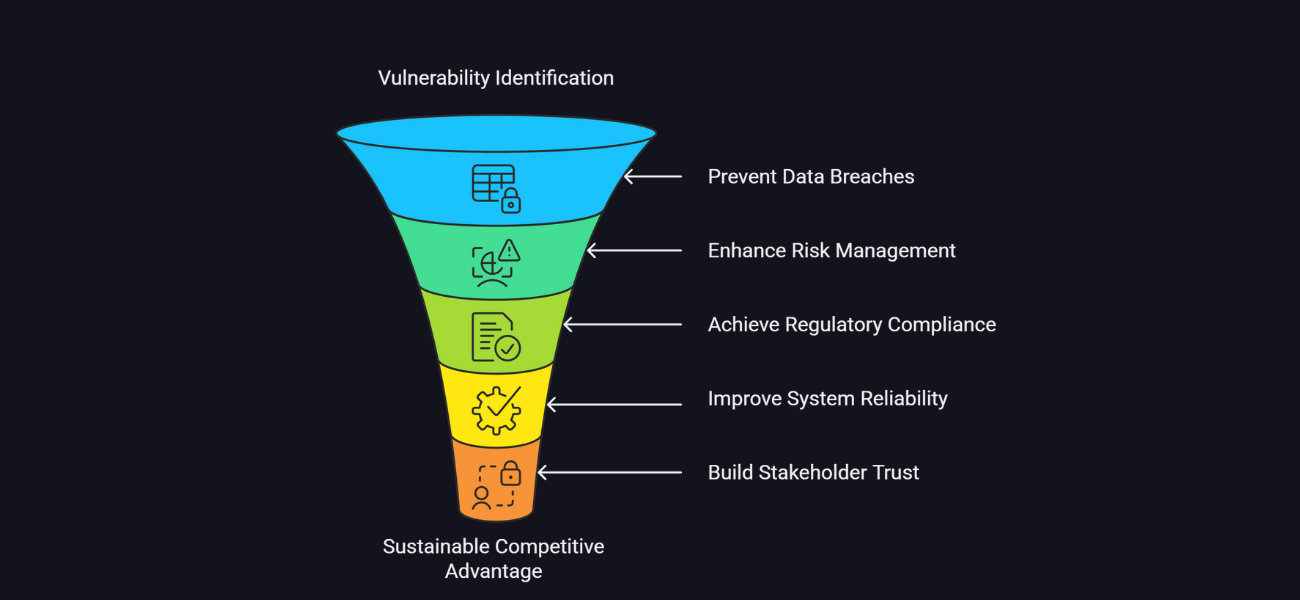
Our security testing uncovers critical flaws in your IT infrastructure, applications, and network systems, allowing you to address them proactively before they can be exploited by cybercriminals. This systematic approach reveals weaknesses across your entire attack surface, providing comprehensive visibility into exploitable vulnerabilities that automated scanning tools frequently miss through manual validation and creative attack scenarios.
By identifying and remediating vulnerabilities through professional security assessments, you protect sensitive customer information, intellectual property, and financial data from unauthorized access. These evaluations help prevent data breaches that average millions in direct costs, regulatory fines, legal expenses, and long-term reputational damage that can devastate customer trust and competitive positioning in your market.
Our vulnerability assessments provide clear understanding of your security posture, helping you prioritize risks based on exploitability and business impact. This intelligence enables effective resource allocation, focusing remediation efforts on the most critical exposures while supporting board-level discussions about acceptable risk tolerance and necessary security investments for business protection.
Many industries face strict security regulations requiring regular security testing. Our compliance-focused approach ensures adherence to standards, helping you avoid substantial fines, legal complications, and regulatory sanctions while demonstrating due diligence to auditors, partners, and customers expecting rigorous security practices.
Identifying and fixing vulnerabilities through systematic security evaluation ensures your systems and applications operate smoothly with minimal security-related downtime. Our assessments reveal configuration weaknesses and architectural flaws that could be exploited to cause denial-of-service conditions, ensuring business continuity and operational resilience against both malicious attacks and accidental failures.
Demonstrating commitment to security through regular assessments helps build confidence with customers, partners, and stakeholders by assuring them their data remains protected. Security certifications and test reports serve as powerful differentiators in competitive sales processes, vendor evaluations, and partnership negotiations where security posture influences business decisions.
Insights gained from our security evaluations inform enhancements to existing security policies, technical controls, and operational practices. The detailed findings and recommendations help you develop more robust security architectures, implement effective compensating controls, and establish security baselines that align with industry best practices and evolving threat landscapes.
Our simulated attack exercises replicate actual adversary methodologies, allowing you to understand how attackers might exploit vulnerabilities and how your defensive controls and incident response capabilities would perform under genuine attack conditions. This realistic assessment reveals gaps in detection, response procedures, and security monitoring that could be addressed before facing actual breaches.
Proactively addressing security issues is significantly more cost-effective than dealing with the aftermath of a breach. Investing in comprehensive security testing helps you avoid the immense costs of incident response, recovery, legal fees, and reputational damage.
In an era where security is a top concern for every business, a verifiably secure posture is a major competitive advantage. Our penetration testing services help you build that posture, making your organization a more attractive and trustworthy partner for clients and customers.
Our structured penetration testing process ensures comprehensive security evaluation through systematic phases that balance thorough assessment with business continuity. As experts in offensive security testing, we guide organizations through each engagement with transparency, precision, and measurable outcomes.
Learn MoreWe initiate every penetration testing engagement with detailed scoping sessions to understand your security objectives, critical assets, and testing constraints. Our team collaborates with stakeholders to define precise testing boundaries, establish rules of engagement, and create realistic timelines aligned with operational requirements.
Our penetration testers conduct comprehensive reconnaissance using open-source intelligence (OSINT), network mapping, and service enumeration. We gather information about your digital footprint, identify exposed assets, and map your attack surface to understand potential entry points that adversaries might exploit.
We execute systematic vulnerability identification using automated scanning tools and manual testing techniques. Our ethical hackers analyze discovered weaknesses within your business context, evaluating exploitability and potential impact to prioritize findings based on actual threat to your operations.
Our penetration testing team attempts to exploit identified vulnerabilities to demonstrate real-world impact and assess defense effectiveness. We perform privilege escalation, lateral movement, and persistence establishment while maintaining controlled approaches that protect system integrity and data confidentiality.
We deliver detailed penetration testing reports containing executive summaries, technical findings, and prioritized remediation recommendations. Our documentation includes reproduction steps, evidence screenshots, and strategic guidance that empowers both technical and business teams to implement effective countermeasures.
Following remediation implementation, we conduct focused retesting to validate fix effectiveness and ensure vulnerabilities have been properly addressed. Our verification confirms that patches and configuration changes successfully eliminate identified weaknesses without introducing new security gaps or operational issues.
Understanding penetration testing helps you make informed security decisions. Here are detailed answers to common questions organizations ask when evaluating professional security testing services.
A vulnerability assessment uses automated tools to scan for and report known vulnerabilities. A penetration test goes further, with our experts manually attempting to exploit those vulnerabilities to determine the real-world risk and potential impact of a breach.
The cost depends on the scope and complexity of the target environment, including the number of applications, servers, or IP addresses. We provide a custom quote after a detailed scoping call to understand your specific needs and objectives.
A typical engagement lasts from one to four weeks, depending on the scope. A small web application test may take a few days, while a comprehensive red team operation can span several weeks. We establish a clear timeline during the planning phase.
The right test depends on your goals. An External Network Test is crucial for perimeter security. A Web Application Test is vital for securing online platforms. An Internal Network Test helps defend against insider threats. We recommend a consultation to help you select the tests that best align with your specific risks and compliance needs.
Our testers hold a range of elite industry certifications, including Offensive Security Certified Professional (OSCP), CREST Registered Penetration Tester (CRT), Certified Ethical Hacker (CEH), and Certified Information Systems Security Professional (CISSP).
Our primary goal is to identify vulnerabilities without causing any operational disruption. We use non-destructive testing techniques and coordinate closely with your IT team to schedule tests during low-traffic periods to minimize any potential impact.
Protecting your data is our highest priority. All sensitive information discovered is encrypted, stored in secure, isolated environments, and communicated only through encrypted channels. Our strict data handling protocols ensure confidentiality, and all client data is securely destroyed post-engagement.
You will receive a detailed report containing an executive summary for leadership, a technical breakdown of each vulnerability with proof-of-concept evidence, and prioritized, actionable steps for remediation. All reports are audit-ready for compliance purposes.
Yes. All of our penetration testing engagements include retesting at no additional cost. Once your team has remediated the findings, we will re-test to validate that the vulnerabilities have been successfully patched and the risk has been eliminated.
Our tests are designed to meet the specific requirements of major compliance frameworks. We identify vulnerabilities that would violate standards like PCI DSS, HIPAA, SOC 2, or ISO 27001 and provide the documentation needed to demonstrate due diligence to auditors.
Absolutely. We specialize in cloud security penetration testing. Our experts assess for common cloud misconfigurations, insecure API keys, IAM policy weaknesses, and vulnerabilities in containerized environments to secure your cloud-native and hybrid infrastructure.
Automated scanners only find known vulnerabilities and often produce false positives. Our human experts can identify complex business logic flaws, chain together low-severity vulnerabilities into a critical risk, and think creatively like a real attacker.
Here is the tech stack used by our team while offering IT development services:
Explore our featured content on different industries that you may find helpful.